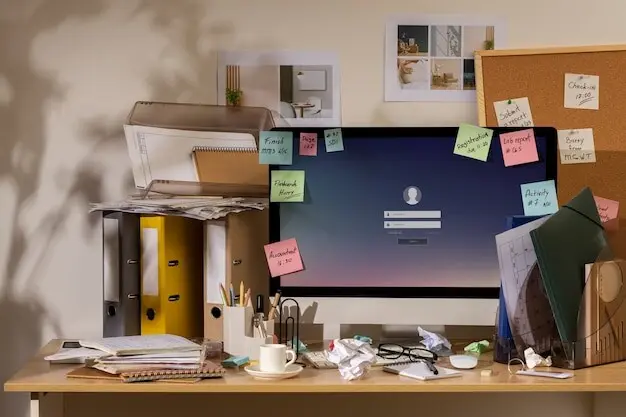
Turn Chaos into Clickless Order
Today, we focus on automating Desktop and Downloads cleanup with scripts and rules, transforming those constantly cluttered folders into calm, predictable spaces. You will learn simple patterns that prevent mess before it accumulates, reliable safeguards that protect your files, and practical steps to get results in minutes. Expect real stories, repeatable checklists, and encouragement to share your wins so others can benefit from your streamlined, stress‑free setup.
See the Mess, Design the Map
Before any line of code or clever rule, clarity about how clutter happens will save hours. Notice what repeatedly lands on your Desktop and in Downloads: screenshots, PDFs, images, invoices, installers, and archives. Understand when files arrive, which ones deserve immediate attention, and which can be routed away. By sketching a simple flow—arrive, inspect, categorize, move—you can turn frantic searching into effortless retrieval, reducing friction and making your workspace naturally support deep, focused work every single day.
Audit Your Patterns
Spend a week observing what appears and what lingers. Capture counts of file types, note typical sizes, and mark the times when clutter spikes, like after meetings or nightly downloads. This gentle audit suggests obvious categories, such as media, documents, and installers, and reveals a few special cases worth white‑listing. When repeated realities are visible, your scripts and rules simply reflect them, sliding files into sensible homes while you keep creating instead of endlessly tidying.
Group by Type and Time
Simple heuristics carry surprising power. Group by extension to separate screenshots, images, audio, archives, and executables. Add time windows to sweep recent files into a staging area for quick review, while older items automatically nest into date‑based folders you can browse without thinking. This pairing—type plus time—prevents piles from forming, shortens search paths, and keeps your most relevant, fresh material at hand without burying long‑term references you rarely touch.
Script Foundations That Respect Your Files
Automation should be considerate, reversible, and boringly dependable. Start small with scripts that copy instead of move, print logs, and avoid overwriting. Whether you use Bash, PowerShell, or Python, write in clear, testable steps. Prefer idempotent operations, where running twice changes nothing unexpectedly. Protect edge cases like duplicate names or half‑downloaded files. Treat your data with kindness, and your confidence will grow as reliably as your desktop shrinks from chaotic collage to deliberate, tidy canvas.
Pick a Friendly Language
Choose what feels natural on your system: Bash or zsh for macOS and Linux, PowerShell for Windows, Python everywhere. Favor built‑in file operations and robust globbing. Reach for libraries like pathlib or shutil in Python, and the FileSystemObject in PowerShell. The friendlier the language feels, the more likely you will refine, extend, and actually maintain your setup rather than abandon it after the first tricky edge case appears at 11 p.m.
Write Safe, Idempotent Movers
Design scripts to detect duplicates, append timestamps, or create non‑colliding filenames. Use temporary paths while copying, then atomically move to final destinations to avoid partial writes. When a file already exists, skip with a clear message or create a versioned sibling. Being idempotent means you can rerun after a crash or tweak rules without fear. Your future self will silently thank past you every time nothing surprising happens during a routine cleanup.
Test on a Sandbox First
Before touching real files, generate a mock Desktop and Downloads with fake images, documents, archives, and intentionally tricky names. Run scripts in dry‑run mode, print planned actions, and verify outcomes against expectations. Gradually introduce real files while still copying instead of moving. Only when results are predictably boring should you enable deletes or permanent moves. This calm, incremental approach builds trust faster than any tutorial promise or heroic, one‑shot weekend refactor.
Let Rules and Schedules Do the Lifting
After scripts behave, let automation engines trigger them. Real‑time watchers notice new files; schedulers handle periodic sweeps. On macOS, consider LaunchAgents, Hazel, or folder actions; on Windows, Task Scheduler, PowerShell’s FileSystemWatcher, or Power Automate Desktop; on Linux, inotify and systemd timers. With triggers humming quietly, your folders self‑organize while you think about actual work. The secret is combining precise matching with generous safety, then documenting when and why each rule fires.
Safety Nets, Logs, and Easy Undo
Automation earns trust when recovery is obvious. Keep moves reversible by sending deletions to Trash or Recycle Bin first. Maintain readable logs with timestamps, actions, and source‑destination pairs. Snapshot critical folders before bigger refactors. Record every assumption inside comments. Share a simple rollback checklist with future you. When mistakes are survivable, experimentation feels playful, iteration accelerates, and your system remains an ally rather than a thrilling, untested stunt that scares everyone away from improvements.

Smart, Consistent Filenames
Adopt a predictable pattern: date, identifier, short description, and version, separated with dashes for readability. Example: 2026‑03‑17‑client‑moodboard‑v2.png. Use scripts to normalize spacing, replace ambiguous characters, and append unique suffixes when duplicates appear. This structure turns your search bar into a superpower, and makes synchronized folders conflict less. Even if you forget where something lives, a quick partial name gets you there without clicking through endless nests or guessing old folder paths.

Metadata as a Compass
Sort beyond extensions by reading metadata. Route camera images using EXIF dates and lens info, file PDFs by author or subject fields, and group audio by bitrate or tags. When metadata is sparse, enrich it during staging with lightweight tools. These contextual clues drive accurate placement even when filenames are generic. Your rules become more resilient, and the final structure feels logical to future collaborators who never saw the original chaotic inflow you tamed.
Trust but Verify Downloads
Treat fresh downloads with cautious optimism. Send executables to a quarantine folder, verify checksums, and allow only signed packages to graduate. For documents, run quick scans or sandbox previews before movement. Tag suspicious items for manual review and expiration. This balanced approach keeps convenience high without naively trusting everything. Security becomes a quiet companion to order, and you stop associating automation with risk because every step is explicit, reviewable, and backed by clear evidence.